Blog
Blog Posts
Business Technology Services Explained
Embrace business technology services to not just survive but thrive in the modern business landscape. Your investment today is the foundation of your success tomorrow.
Business IT Services: Essential Guide
Nowadays, business IT services are not just a luxury but a necessity. The seamless operation of IT infrastructure is critical for companies to stay competitive, efficient, and secure.
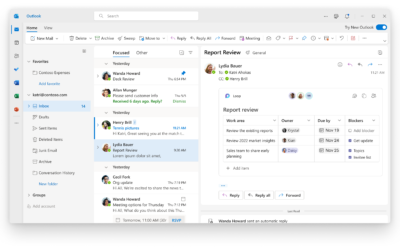
How to Recall an Email in Outlook
Here’s a step-by-step guide on how to recall an email in Outlook:
Open Outlook and Go to Sent Items
Microsoft 365 vs Google Workspace
Selecting the right productivity suite is crucial for any business. Two major contenders dominate the market: Microsoft 365 vs Google Workspace. Both offer a range of tools designed…
Email Bounceback Explained
Understanding what an email bounceback is, the common types, reasons behind them, and how to prevent them can significantly improve your email deliverability rates.
Troubleshooting Steps: Dell Server Will Not Power On
When a Dell server will not power on, it can be a daunting situation. However, by following these troubleshooting steps, you can systematically identify and possibly resolve the issue. Performing a power drain,
Office365 Migration : Comprehensive Guide
Among these transformations, migrating to Office365 has emerged as a pivotal change for businesses aiming to enhance their operational efficiency and communication dynamics.
Guide to Data Backups and Disaster Recovery
Data backups stand as the frontline defense in this battle, ensuring that your organization can recover from any disaster, including cyber attacks like ransomware. The importance of investing in robust data backups and disaster recovery plans cannot be overstated, offering a lifeline to businesses aiming for continuity amidst chaos.
Fake Email Orders and How to Stop Them
A concerning trend that has gained momentum is the proliferation of fake email orders. This phenomenon is not just a nuisance; it’s a sophisticated scam operation designed to deceive individuals and businesses alike, often with significant financial consequences.
The Rising Threat of CEO Fraud
In today’s fast-paced business world, the threat of cyber crime looms larger than ever, with CEO fraud emerging as one of the most sophisticated and financially damaging scams. CEO fraud, also known as Business Email Compromise (BEC), targets businesses of all sizes
The Crucial Role of a Business Firewall
A business firewall acts as the first line of defense, safeguarding your company’s network by filtering incoming and outgoing traffic based on a set of security rules. This post delves into the importance of choosing the right business firewall and highlights some common and popular providers like Fortigate, Cisco Meraki, and Unifi.
Best Business Spam Filter: 2024 Guide
The quest for the “best business spam filter” is more than a search—it’s a mission to protect your digital ecosystem. In this comprehensive guide, we delve into the most widely acclaimed business spam filters, including ProofPoint, Microsoft Defender, SpamTitan, and MailProtector, and
Best Business Antivirus: 2024 Guide
The quest for the “best business antivirus” is on every business owner’s mind, seeking robust protection against malware, ransomware, and other cyber threats. This guide is designed to help you navigate through the most widely used business antiviruses, including Malwarebytes, BitDefender, and SentinelOne, providing insights into each to ensure you make an informed decision.
Growing Threat of Healthcare Ransomware
In the rapidly evolving digital landscape, healthcare ransomware has emerged as a formidable threat to the integrity and functionality of medical institutions worldwide. This specific type of cyberattack involves the encryption of an organization’s data by malicious actors, who then demand a ransom in exchange for the decryption key.
Best Accounting Software for CPAs and Accounting Firms
For CPAs and accounting firms aiming to streamline their operations and enhance productivity, selecting the best accounting software is a pivotal decision. This comprehensive guide is dedicated to exploring the most widely used accounting software
The Best Trucking Software To Use
In today’s ever changing world of logistics and transportation, trucking companies are always on the lookout for the most efficient ways to manage their operations. With the advent of digital solutions, finding the best trucking software has become a paramount task for these businesses.
Discovering The Best ERP Software
The “best ERP software” isn’t a one-size-fits-all solution; rather, it depends on an organization’s specific needs, size, and industry. This blog post delves into the world of ERP solutions, offering insights into the most widely used options and comparing their advantages and disadvantages.
Enable DKIM on Office365
A lot of providers such as Yahoo have changed their requirements for inbound emails and are now requiring that emails which are sent to their servers have the necessary DNS records before the email is allowed to reach the recipients. One such record is the DKIM record.
If you are trying to figure out how to enable DKIM on Office365, just follow the steps below and you’ll be back to delivering emails in no time.
Why You Should Pick a Local IT Provider
In this guide, we’ll explore why picking a local IT provider such as ATYXIT is not just a smart decision, but a crucial one for both the success and security of your business.
From ESXi Pricing to the Impact of Broadcom Acquisition
In this blog post, we’ll explore the journey of VMware, delve into ESXi pricing, and analyze the implications of the Broadcom acquisition on VMware’s product landscape.
Navigating BYOD Risks and Best Practices
Understanding these risks and implementing best practices is crucial for safeguarding your organization’s assets. Let’s delve into the realm of BYOD risks as well as exploring its significance and the importance of effective management.
Ransomware Recovery: Safeguarding Your Business
Understanding the gravity of this threat and taking proactive measures for ransomware recovery is paramount in safeguarding your business against potential devastation.
Information Security Policy Explained
An Information Security Policy stands as a linchpin in an organization’s cybersecurity framework, guiding the establishment of robust measures to ensure data integrity, confidentiality, and compliance with regulatory requirements.
Securing a Server: A Comprehensive Guide
Securing a server is not merely a technical task; it is a strategic imperative to protect sensitive data, ensure business continuity, and fortify the organization against cyber threats. In this detailed blog article…
We're Here To Help!
Office
Bensenville, IL 60106
Hours
S-S: Closed