Feb 23, 2026 | Business IT News, Business IT Tips
The Hidden Dangers of Using Password Managers In an age where nearly every website requires a login, password managers have become a go-to solution for simplifying online security. They promise to create, store, and manage your passwords safely, but not all promises...

Jan 13, 2026 | Business IT News, Business IT Tips
In 2026, small and mid-sized businesses are under pressure to modernize around AI, cloud, and cybersecurity while keeping costs and risk under control. A provider like ATYXIT can act as a strategic IT partner to plan, implement, and support these changes without...

Oct 21, 2025 | Law IT Tips
Attorneys and law firms operate in an environment where secure, efficient, and reliable IT systems are crucial to their success. The sensitive nature of legal data—from client information to confidential case files—demands not just functional IT, but proactive...

Aug 26, 2025 | Business IT News
The volume of ransomware attacks in 2025 was up by 179% compared to the same period in 2024, according to statistics published by threat intelligence platform provider Flashpoint. The past year has seen significant changes among cyber criminal threat actors with...
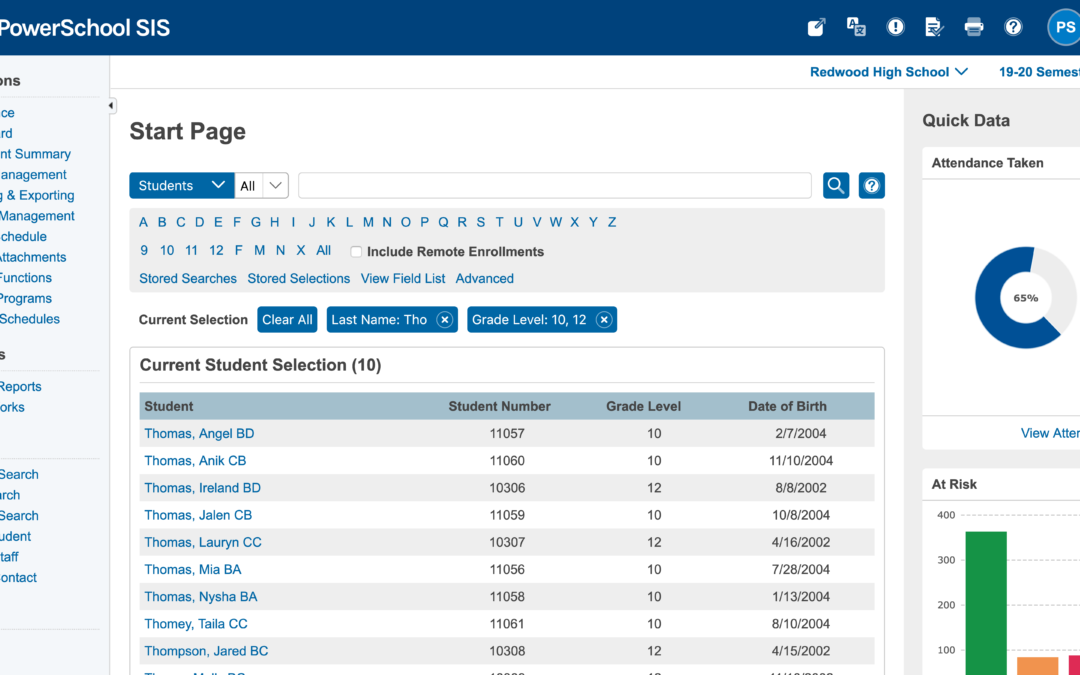
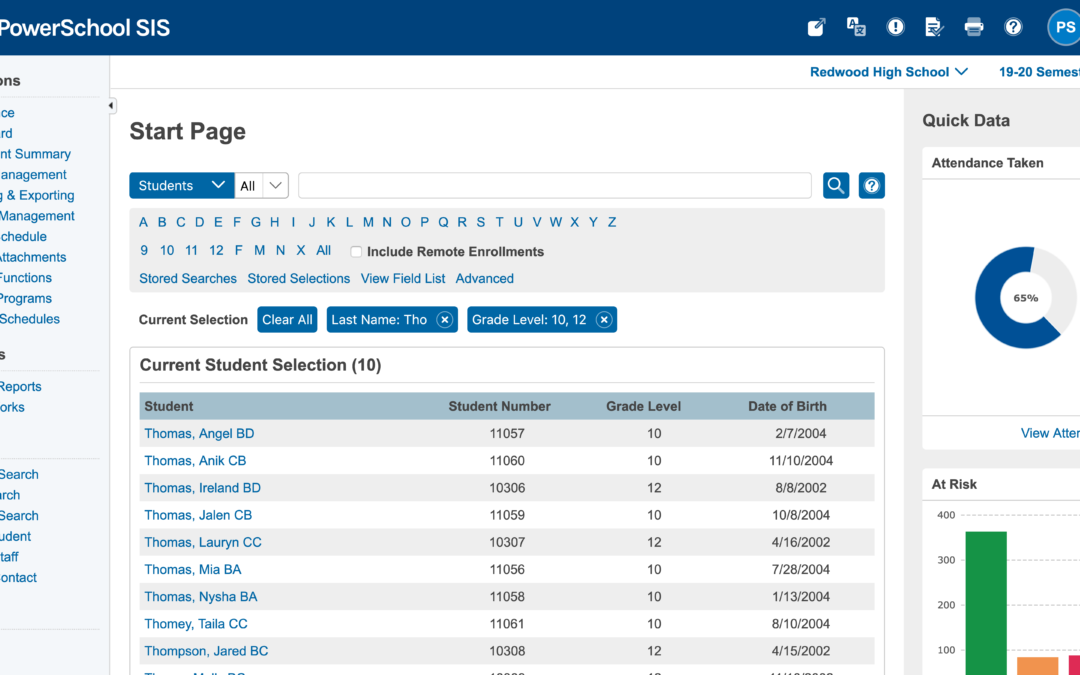
Feb 6, 2025 | Business IT News
The recent PowerSchool data breach has sent shockwaves through the education sector, exposing sensitive information of millions of students and teachers across North America. This massive cyberattack, discovered in late December 2024, has affected thousands of school...