Jan 22, 2025 | Business IT Tips
Implementing business 2FA (two-factor authentication) is a crucial step in enhancing cybersecurity at your organization. Here’s a comprehensive guide with some tips on rolling out 2FA effectively across all your employees: 1. Assess Your Current Security Posture...

Jan 20, 2025 | Business IT Tips, Knowledgebase
PowerShell has become an essential tool for Windows Server and Active Directory management. Here’s a guide to some of the most useful PowerShell commands for these types of environments that are guaranteed to make both your life and management easier. Active...

Jan 18, 2025 | Business IT Tips
The Crucial Role of Employee Cybersecurity Training in Protecting Businesses In today’s digital landscape, where cyber threats are becoming increasingly sophisticated and prevalent, employee cybersecurity training alongside immutable backups has emerged as a...
Jan 16, 2025 | Business IT Tips, Security Advisories
Data backups serve as a critical line of defense for businesses against the growing threat of ransomware attacks. As cyber crime costs are projected to reach $10.5 trillion annually by 2025, organizations must implement and periodically test robust data protection...
Oct 24, 2024 | Business IT Tips, Security Advisories
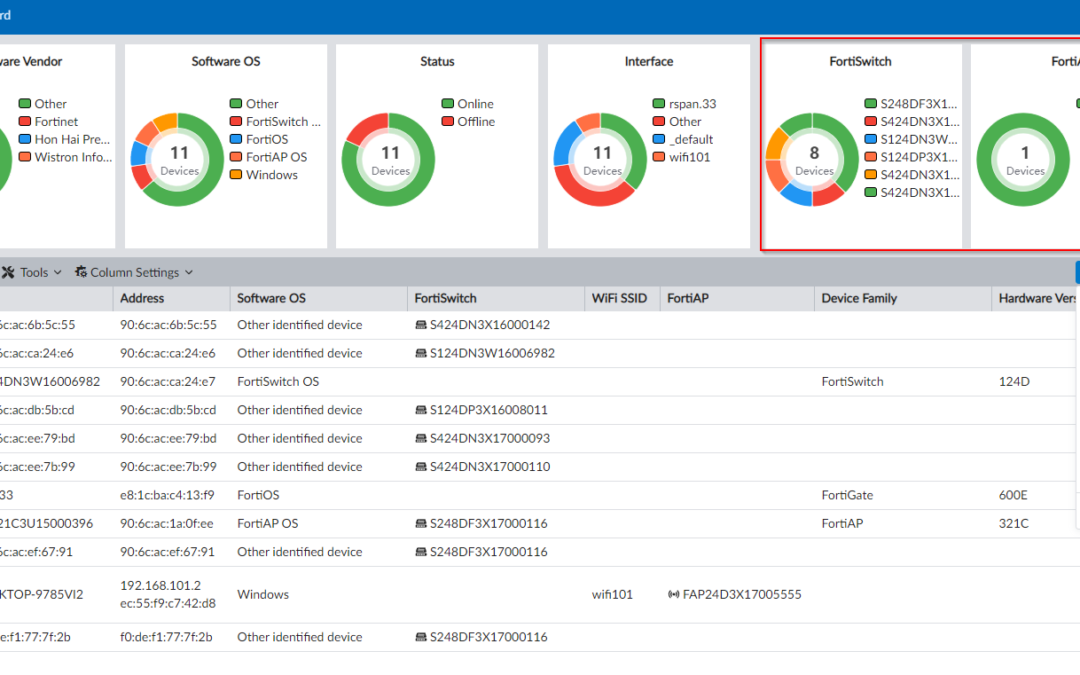
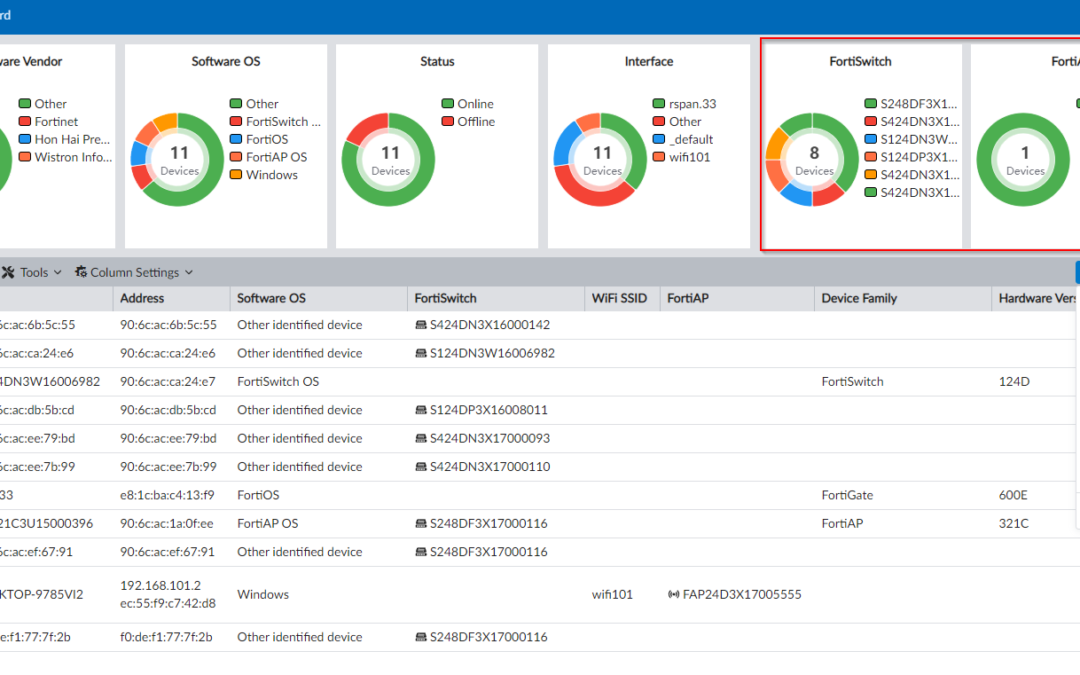
In today’s digital landscape, cybersecurity threats are evolving at an unprecedented pace, posing significant risks to businesses of all sizes. Recently, a critical vulnerability in Fortinet’s FortiManager, identified as CVE-2024-47575, has highlighted the...

Aug 23, 2024 | Business IT Tips
In the rapidly evolving business landscape, digital transformation is no longer a luxury but a necessity for organizations seeking to remain competitive and innovative. As a top priority for business decision-makers, digital transformation involves integrating digital...